Written by Roman Peťura on Friday 17 June 2022 in the category Release with the tags Headline, Security.
A new version of ICR-OS (Conel OS), firmware for the Advantech routers, is out!
A patch-level release mainly brings many security fixes, improvements, and updates. You are welcome to check out the Release Notes for the detailed changelog.
A few highlighted points from the changelog:
Written by Jan Svoboda on Tuesday 7 June 2022 in the category Release with the tags DMP.
The new, 2.4.3, version of the WebAccess/DMP has been released.
It brings UI improvements, appearance changes, and bug fixes.
Details can be found in Release Notes, which are available here.
Written by Miloslav Bien on Monday 6 June 2022 in the category Newsletter.

New Router AppTR-069 for v2, v2i, v3, and v4 Advantech routers has been released in May 2022. Router Technical Report 069 (TR-069) is a technical specification of the Broadband Forum that defines an application layer protocol for remote management and provisioning of customer premises equipment (CPE) connected to an Internet Protocol (IP) network.
TR-069 uses the CPE WAN Management Protocol (CWMP) which provides support functions for auto-configuration, software or firmware image management, software module management, ...
Written by Miloslav Bien on Wednesday 1 June 2022 in the category Newsletter.
Pleased to share the information we have made a connection to WebAccess/DMP even more intuitive and easier for all router users. We also serve customer requests for zero-touch provisioning and management via our Advantech WebAccess/DMP platform. Visit the WebAccess/DMP webpage for more information and ideas this advanced enterprise-grade platform solution for provisioning, monitoring, managing, and configuring Advantech routers and IoT gateways would bring to you.
Connection from routers to WebAccess/DMP is to be activated for all routers of the v2i platform, v3 platform, and v4 platform directly ...
Written by Miloslav Bien on Friday 20 May 2022 in the category Release.

We are glad to share the information that we have boosted ICR-2400 and ICR-2600 cellular router lines for the new guys recently. Entry-level 4G cellular router platform now covers by beside standard 4G bands also LTE 450 MHz, Private LTE bands or LPWA communication on LTE Cat-M and NB/IoT frequencies. See the list of newcomers below.
Written by Roman Peťura on Friday 22 April 2022 in the category Release with the tags Headline, Security.
A new version of ICR-OS (Conel OS), firmware for the Advantech routers, is out!
A patch-level release mainly brings many security fixes, improvements, and updates. You are welcome to check out the Release Notes for the detailed changelog.
A few highlighted points from the changelog:
OpenVPN TAP mode is now supported.
Persistent System Log storage to the eMMC memory is supported.
The router identification string, used for the remote sys logging, is now configurable.
Added support for the dd program, which can be used to copy a file and convert the data format in the ...
Written by Marek Černocký on Wednesday 30 March 2022 in the category Release with the tags IIoT, Node-RED, Router App, Development.

Among the new features we can highlight for example the configurable properties of the input ...
Written by Miloslav Bien on Wednesday 16 March 2022 in the category Newsletter.

Two new software Router Apps (User modules) have been released a few days ago. Let's go to look a little bit closer to them.
MQTT Manager is a Router App for controlling and monitoring Advantech routers via the MQTT protocol. It is possible to send through a specific MQTT message commands to perform specific actions – for example change binary output status on router. User can also track status of the router by subscribing to ...
Written by Miloslav Bien on Tuesday 15 March 2022 in the category Newsletter.
We are glad to share the information that we developed new models within our ICR-4400 family to avoid the temporary unavailability of WIFI chips from the supplier. Those new models keep the same high-end WIFI parameters as the original models and the only drawback is a slightly decreased temperature range for the router reaching -40 to +60°C.
The new router models are marked as ICR-4453W1 + ICR-4453W1S for 5G, ICR-4434W1 + ICR-4434W1S for ...
Written by Miloslav Bien on Wednesday 16 February 2022 in the category Newsletter.
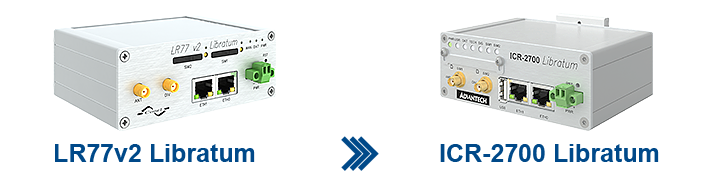
We are glad to share information that cellular routers ICR-2734 are close to mass production planned for April 2022. ICR-2734 Libratum provides enhanced replacement of Advantech´s cellular router best seller LR77 v2 Libratum bringing advantages to customers in the modern hardware platforms. The scale of applications in the industrial and public sector now grows with higher power hardware providing optimal LTE/4G cellular connectivity.